A) US-STANDARD uses eventual consistency and it can take time for an object to be readable in a bucket
B) Objects in Amazon S3 do not become visible until they are replicated to a second region.
C) US-STANDARD imposes a 1 second delay before new objects are readable.
D) You exceeded the bucket object limit, and once this limit is raised the object will be visible.
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which of the following are valid SNS delivery transports? (Choose two.)
A) HTTP
B) UDP
C) SMS
D) DynamoDB
E) Named Pipes
G) A) and E)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A Developer is writing a mobile application that allows users to view images from an S3 bucket. The users must be able to log in with their Amazon login, as well as Facebook® and/or Google® accounts. How can the Developer provide this authentication functionality?
A) Use Amazon Cognito with web identity federation.
B) Use Amazon Cognito with SAML-based identity federation.
C) Use AWS IAM Access/Secret keys in the application code to allow Get* on the S3 bucket. Use AWS IAM Access/Secret keys in the application code to allow Get* on the S3 bucket.
D) Use AWS STS AssumeRole in the application code and assume a role with Get* permissions on the S3 bucket. Use AWS STS AssumeRole in the application code and assume a role with permissions on the S3 bucket.
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A Developer needs temporary access to resources in a second account. What is the MOST secure way to achieve this?
A) Use the Amazon Cognito user pools to get short-lived credentials for the second account.
B) Create a dedicated IAM access key for the second account, and send it by mail.
C) Create a cross-account access role, and use sts:AssumeRole API to get short-lived credentials. Create a cross-account access role, and use sts:AssumeRole API to get short-lived credentials.
D) Establish trust, and add an SSH key for the second account to the IAM user.
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A Developer has implemented a Lambda function that needs to add new customers to an RDS database that is expected to run hundreds of times per hour. The Lambda function is configured to use 512MB of RAM and is based on the following pseudo code: 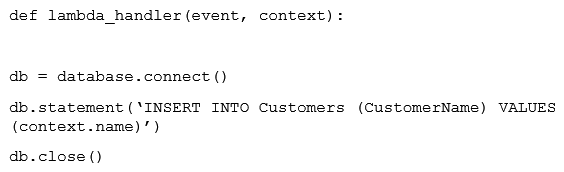 After testing the Lambda function, the Developer notices that the Lambda execution time is much longer than expected. What should the Developer do to improve performance?
After testing the Lambda function, the Developer notices that the Lambda execution time is much longer than expected. What should the Developer do to improve performance?
A) Increase the amount of RAM allocated to the Lambda function, which will increase the number of threads the Lambda can use.
B) Increase the size of the RDS database to allow for an increased number of database connections each hour.
C) Move the database connection and close statement out of the handler. Place the connection in the global space.
D) Replace RDS wit Amazon DynamoDB to implement control over the number of writes per second.
F) B) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
An application under development is required to store hundreds of video files. The data must be encrypted within the application prior to storage, with a unique key for each video file. How should the Developer code the application?
A) Use the KMS Encrypt API to encrypt the data. Store the encrypted data key and data. Use the KMS Encrypt API to encrypt the data. Store the encrypted data key and data.
B) Use a cryptography library to generate an encryption key for the application. Use the encryption key to encrypt the data. Store the encrypted data.
C) Use the KMS GenerateDataKey API to get a data key. Encrypt the data with the data key. Store the encrypted data key and data. GenerateDataKey API to get a data key. Encrypt the data with the data key. Store the encrypted data key and data.
D) Upload the data to an S3 bucket using server side-encryption with an AWS KMS key.
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company wants to implement authentication for its new REST service using Amazon API Gateway. To authenticate the calls, each request must include HTTP headers with a client ID and user ID. These credentials must be compared to authentication data in an Amazon DynamoDB table. What MUST the company do to implement this authentication in API Gateway?
A) Implement an AWS Lambda authorizer that references the DynamoDB authentication table
B) Create a model that requires the credentials, then grant API Gateway access to the authentication table
C) Modify the integration requests to require the credentials, then grant API Gateway access to the authentication table
D) Implement an Amazon Cognito authorizer that references the DynamoDB authentication table
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
An application deployed on AWS Elastic Beanstalk experiences increased error rates during deployments of new application versions, resulting in service degradation for users. The Development team believes that this is because of the reduction in capacity during the deployment steps. The team would like to change the deployment policy configuration of the environment to an option that maintains full capacity during deployment while using the existing instances. Which deployment policy will meet these requirements while using the existing instances?
A) All at once
B) Rolling
C) Rolling with additional batch
D) Immutable
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
An on-premises application is implemented using a Linux, Apache, MySQL and PHP (LAMP) stack. The Developer wants to run this application in AWS. Which of the following sets of AWS services can be used to run this stack?
A) Amazon API Gateway, Amazon S3
B) AWS Lambda, Amazon DynamoDB
C) Amazon EC2, Amazon Aurora
D) Amazon Cognito, Amazon RDS
E) Amazon ECS, Amazon EBS
G) A) and E)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A developer is changing the configuration for a CPU-intensive AWS Lambda function that runs once an hour. The function usually takes 45 seconds to run, but sometimes the run time is up to 1 minute. The timeout parameter is set to 3 minutes, and all other parameters are set to default. The developer needs to optimize the run time of this function. Which solution will meet this requirement?
A) Redeploy the function within the default VPC.
B) Increase the function's memory.
C) Redeploy the function by using Lambda layers.
D) Increase the function's reserved concurrency.
F) All of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A gaming company is developing a mobile game app for iOS and Android platforms. This mobile game securely stores user data locally on the device. The company wants users to have the ability to use multiple devices for the game. The company needs to synchronize user data across devices without creating a backend application. Which AWS service or feature should the company use to meet these requirements?
A) AWS Lambda@Edge
B) Amazon S3 Transfer Acceleration
C) Amazon DynamoDB Accelerator (DAX)
D) AWS Amplify with AWS AppSync
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
An application stores images in an S3 bucket. Amazon S3 event notifications are used to trigger a Lambda function that resizes the images. Processing each image takes less than a second. How will AWS Lambda handle the additional traffic?
A) Lambda will scale out to execute the requests concurrently.
B) Lambda will handle the requests sequentially in the order received.
C) Lambda will process multiple images in a single execution.
D) Lambda will add more compute to each execution to reduce processing time.
F) All of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company requires that AWS Lambda functions written by Developers log errors so System Administrators can more effectively troubleshoot issues. What should the Developers implement to meet this need?
A) Publish errors to a dedicated Amazon SQS queue.
B) Create an Amazon CloudWatch Events event trigger based on certain Lambda events.
C) Report errors through logging statements in Lambda function code.
D) Set up an Amazon SNS topic that sends logging statements upon failure.
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A developer is migrating code to an AWS Lambda function that will an Amazon Aurora MySQL database. What is the MOST secure way to authenticate the function to the database?
A) Store the database credentials as encrypted parameters in AWS Systems Manager Parameters Store. Obtain the credentials from Systems Manager when the Lambda function needs to connect to the database.
B) Store the database credentials in AWS Secrets Manager. Let Secrets Manager handle the rotation of the credentials, as required.
C) Store the database credentials in an Amazon S3 bucket that has a restrictive bucket policy for the Lambda role when accessing the credentials. Use AWS KMS to encrypt the data.
D) Create a policy with rds-db:connect access to the database and attach it to the role assigned to the Lambda function.
F) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
An application overwrites an object in Amazon S3, and then immediately reads the same object. Why would the application sometimes retrieve the old version of the object?
A) S3 overwrite PUTS are eventually consistent, so the application may read the old object.
B) The application needs to add extra metadata to label the latest version when uploading to Amazon S3.
C) All S3 PUTS are eventually consistent, so the application may read the old object.
D) The application needs to explicitly specify latest version when retrieving the object.
F) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A developer is building an application using an Amazon API Gateway REST API backed by an AWS Lambda function that interacts with an Amazon DynamoDB table. During testing, the developer observes high latency when making requests to the API. How can the developer evaluate the end-to-end latency and identify performance bottlenecks?
A) Enable AWS CloudTrail logging and use the logs to map each latency and bottleneck.
B) Enable and configure AWS X-Ray tracing on API Gateway and the Lambda function. Use X-Ray to trace and analyze user requests.
C) Enable Amazon CloudWatch Logs for the Lambda function. Enable execution logs for API Gateway to view and analyze user request logs.
D) Enable VPC Flow Logs to capture and analyze network traffic within the VPC.
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company has implemented AWS CodeDeploy as part of its cloud native CI/CD stack. The company enables automatic rollbacks while deploying a new version of a popular web application from in-place to Amazon EC2. What occurs if the deployment of the new version fails due to code regression?
A) The last known good deployment is automatically restored using the snapshot stored in Amazon S3.
B) CodeDeploy switches the Amazon Route 53 alias records back to the known good green deployment and terminates the failed blue deployment.
C) A new deployment of the last known version of the application is deployed with a new deployment ID.
D) AWS CodePipeline promotes the most recent deployment with a SUCCEEDED status to production.
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A Developer has created a new AWS IAM user that has s3:putObject permission to write to a specific Amazon S3 bucket. This S3 bucket uses server-side encryption with AWS KMS managed keys (SSE-KMS) as the default encryption. Using the access key and secret key of the IAM user, the application received an access denied error when calling the PutObject API. How can this issue be resolved?
A) Update the policy of the IAM user to allow the s3:Encrypt action.
B) Update the bucket policy of the S3 bucket to allow the IAM user to upload objects.
C) Update the policy of the IAM user to allow the kms:GenerateDataKey action.
D) Update the ACL of the S3 bucket to allow the IAM user to upload objects.
F) All of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A Developer executed a AWS CLI command and received the error shown below: 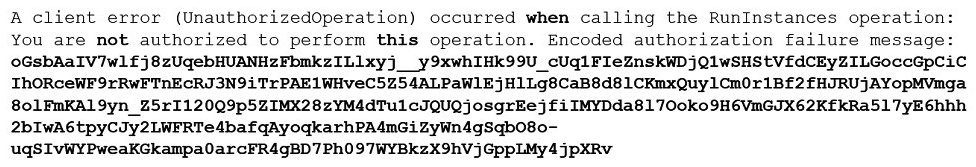 What action should the Developer perform to make this error human-readable?
What action should the Developer perform to make this error human-readable?
A) Make a call to AWS KMS to decode the message.
B) Use the AWS STS decode-authorization-message API to decode the message.
C) Use an open source decoding library to decode the message.
D) Use the AWS IAM decode-authorization-message API to decode this message.
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company is migrating from a monolithic architecture to a microservices-based architecture. The Developers need to refactor the application so that the many microservices can asynchronously communicate with each other without impacting performance. Use of which managed AWS services will enable asynchronous message passing? (Choose two.)
A) Amazon SQS
B) Amazon Cognito
C) Amazon Kinesis
D) Amazon SNS
E) Amazon ElastiCache
G) A) and D)
Correct Answer

verified
Correct Answer
verified
Showing 101 - 120 of 470
Related Exams